FoxBleed
If you have been living under a rock recently:
Heartbleed is a bug in OpenSSL that allows anyone on the internet to read chunks of memory on vulnerable servers, that may include your private data, too.
Since I also visit not-so-famous websites (whose owners might not have heard about the vulnerability) on a regular basis, I wanted to ease the checking procedure, so I could identify all vulnerable websites I'm visiting and notify those responsible.
Therefore, I quickly hacked a Firefox addon together, that may also help you during your journey of securing your Internet and as a result your private data.
You can install FoxBleed from https://addons.mozilla.org/de/firefox/addon/foxbleed/ or this server.
Pictures
Addon's README.md:
Description
This addon eases the checking procedure for the Heartblug Bug, so the user can identify all vulnerable websites he's visiting and notify those responsible.
It achieves this by automatically checking the websites you are visiting whether they are affected by the HeartBleed Vulnerability and notifies you in case they are.
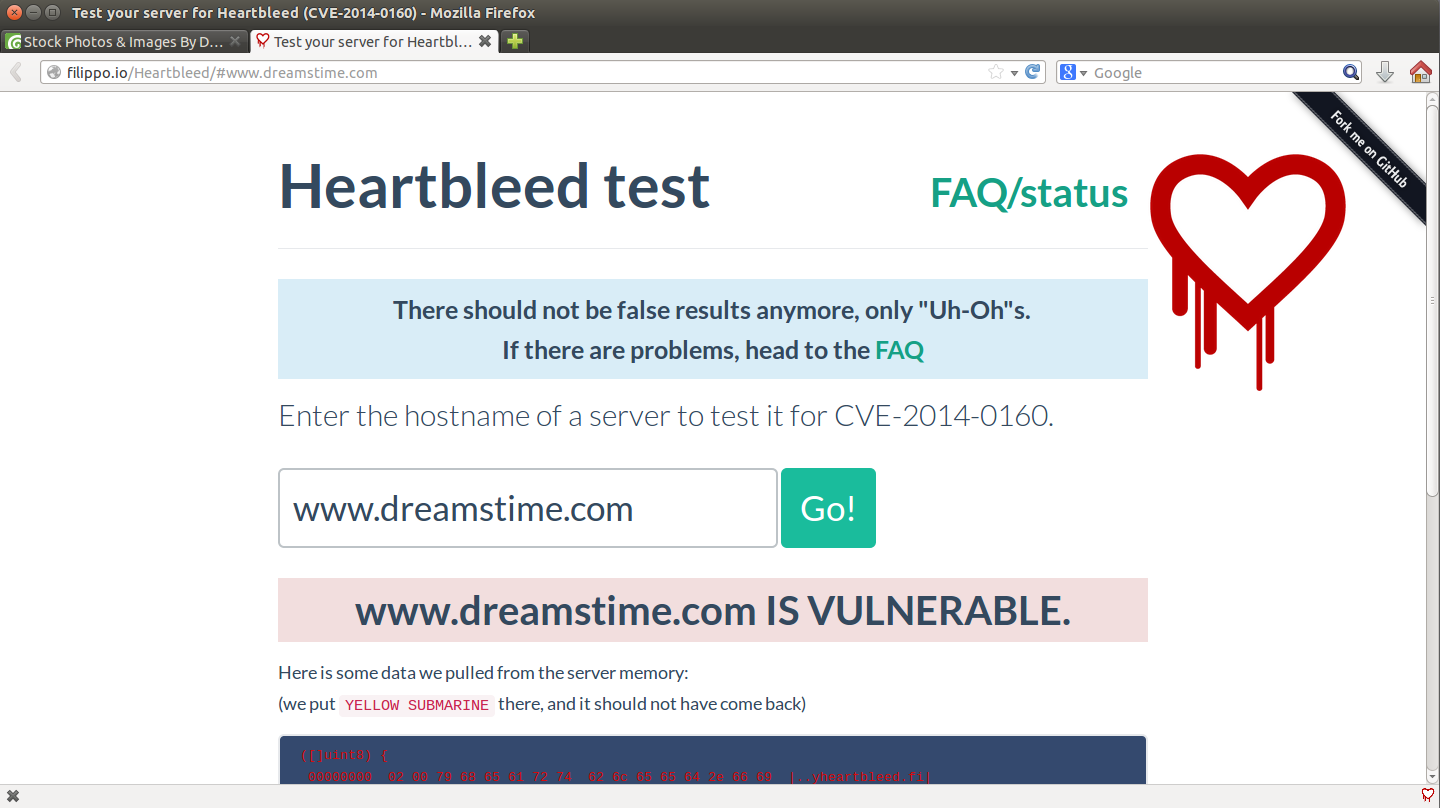
The check works by uploading only the domain name to the filippo.io/Heartbleed/-API and parsing the results.
In case you come across an affected website, you should immediately notify the website owner! Not only the website itself is exposed to danger, but also also your private data!
If you're interested in a version for Google Chrome, you can find it here:
https://chrome.google.com/webstore/detail/chromebleed/eeoekjnjgppnaegdjbcafdggilajhpic
Features - if one can even call it that:
- when visiting a vulnerable website for the first time of the current browser session, a new tab with the corresponding http://filippo.io/Heartbleed/#-site is opened
- indicates exposure to the vulnerability with a filled HeartBleed icon in the bottom right corner
- checks each domain name only once per browser session
You can learn more about the vulnerability at http://heartbleed.com/: "The Heartbleed Bug is a serious vulnerability in the popular OpenSSL cryptographic software library. [...] The Heartbleed bug allows anyone on the Internet to read the memory of the systems protected by the vulnerable versions of the OpenSSL software. This compromises the secret keys used to identify the service providers and to encrypt the traffic, the names and passwords of the users and the actual content. This allows attackers to eavesdrop on communications, steal data directly from the services and users and to impersonate services and users."
(cc) quickly hacked together with love by Fabian Bräunlein